Ingress
组成
ingress controller
将新加入的Ingress转化成Nginx的配置文件并使之生效
ingress服务
将Nginx的配置抽象成一个Ingress对象,每添加一个新的服务只需写一个新的Ingress的yaml文件即可
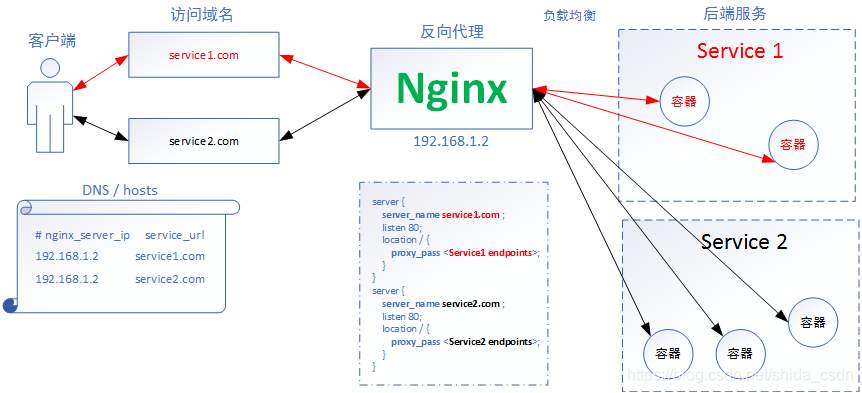
工作原理
1.ingress controller通过和kubernetes api交互,动态的去感知集群中ingress规则变化,
2.然后读取它,按照自定义的规则,规则就是写明了哪个域名对应哪个service,生成一段nginx配置,
3.再写到nginx-ingress-control的pod里,这个Ingress controller的pod里运行着一个Nginx服务,控制器会把生成的nginx配置
写入/etc/nginx.conf文件中,
4.然后reload一下使配置生效。以此达到域名分配置和动态更新的问题。
访问原理
Ingress-nginx与Service之间通过匹配serviceName绑定,Service相当于给外界提供访问pod的端口,如果不采用ingress-nginx,
那么是由kube-proxy实现4层代理,只能通过ip访问,所以由NodePort的类型将端口暴露。如果采用ingress-nginx相当于在Service
前面加了一层代理,访问会先经过ingress-nginx,这样Service的类型就不需要变更为NodePort
测试部署
ingress-nginx.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
data:
proxy-body-size: 100M
---
kind: ConfigMap
apiVersion: v1
metadata:
name: tcp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: udp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: nginx-ingress-clusterrole
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses/status
verbs:
- update
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: Role
metadata:
name: nginx-ingress-role
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
resourceNames:
# Defaults to "<election-id>-<ingress-class>"
# Here: "<ingress-controller-leader>-<nginx>"
# This has to be adapted if you change either parameter
# when launching the nginx-ingress-controller.
- "ingress-controller-leader-nginx"
verbs:
- get
- update
- apiGroups:
- ""
resources:
- configmaps
verbs:
- create
- apiGroups:
- ""
resources:
- endpoints
verbs:
- get
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: RoleBinding
metadata:
name: nginx-ingress-role-nisa-binding
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: nginx-ingress-role
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: nginx-ingress-clusterrole-nisa-binding
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: nginx-ingress-clusterrole
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: apps/v1
#kind: Deployment
kind: DaemonSet
metadata:
name: nginx-ingress-controller
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
# replicas: 1
selector:
matchLabels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
annotations:
prometheus.io/port: "10254"
prometheus.io/scrape: "true"
spec:
serviceAccountName: nginx-ingress-serviceaccount
containers:
- name: nginx-ingress-controller
image: registry:5000/library/k8s/nginx-ingress-controller:0.25.0_x
args:
- /nginx-ingress-controller
- --configmap=$(POD_NAMESPACE)/nginx-configuration
- --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services
- --udp-services-configmap=$(POD_NAMESPACE)/udp-services
- --publish-service=$(POD_NAMESPACE)/ingress-nginx
- --annotations-prefix=nginx.ingress.kubernetes.io
securityContext:
allowPrivilegeEscalation: true
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
# www-data -> 33
runAsUser: 33
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
ports:
- name: http
containerPort: 80
hostPort: 80
protocol: TCP
- name: https
containerPort: 443
hostPort: 443
protocol: TCP
livenessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
---
ingress.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress
spec:
rules:
- host: www.aaa.com
http:
paths:
- backend:
serviceName: myapp
servicePort: 80
path: /
#serviceName对应service服务名
$ kubectl get svc
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kubernetes ClusterIP 241.254.0.1 <none> 443/TCP 40m
myapp ClusterIP 241.254.50.93 <none> 80/TCP 37m
$ kubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress <none> www.aaa.com 80 25m
#做宿主机host文件
$ cat /etc/hosts
192.168.234.134 www.aaa.com
$ curl www.aaa.com/hostname.html
myapp-deploy-6d4bc5cc76-g7tqw
$ curl www.aaa.com/hostname.html
myapp-deploy-6d4bc5cc76-jg4xf
https部署测试
#自签发证书,可以使用下面的语句,也可以阅读自制https的博客
$ openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/O=aaa/CN=*.aaa.com"
$ ll
总用量 8
-rw-r--r-- 1 root root 1131 9月 19 16:30 tls.crt
-rw-r--r-- 1 root root 1704 9月 19 16:30 tls.key
#导入证书文件到k8s secret(注意这边的nginx-test要和下面ingress.yaml文件中tls相对应)
$ kubectl create -n 名称空间(ingress.yaml所在名称空间,如果是default,可忽略) secret tls nginx-test --cert=tls.crt --key=tls.key
$ kubectl get secret
NAME TYPE DATA AGE
nginx-test kubernetes.io/tls 2 53m
#创建https的ingrss.yaml文件
$ cat ingress.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress
annotations:
nginx.ingress.kubernetes.io/ssl-redirect: "false" #是否开启强制跳转,true/false,默认开启
spec:
tls:
- hosts:
- www.aaa.com
secretName: nginx-test
#多域名配置
#- hosts:
# - www.bbb.com
# secretName: nginx-bbb
rules:
- host: www.aaa.com
http:
paths:
- backend:
serviceName: myapp
servicePort: 80
path: /
#- host: www.bbb.com
# http:
# paths:
# - backend:
# serviceName: myapp3
# servicePort: 80
# path: /
Ingress相关配置
通用配置
| 名称 | 描述 | 值 |
|---|---|---|
| nginx.ingress.kubernetes.io/enable-access-log | 对当前虚拟主机设置是否启用访问日志,默认为真 | true 或 false |
| nginx.ingress.kubernetes.io/server-alias | 为 Nginx 添加更多的主机名,同 Nginx 配置指令 server name | string |
| nginx.ingress.kubernetes.io/app-root | 将当前虚拟主机根目录的访问 302 跳转到当前指定的路径 | string |
| nginx.ingress.kubernetes.io/client-body-buffer-size | 同 Nginx 配置指令 client_body_buffer_size | string |
| nginx.ingress.kubernetes.io/use-regex | 指示在 Ingress 上定义的路径是否使用正则表达式 默认值为 false | true 或 false |
| nginx.ingress.kubernetes.io/custom-http-errors | 根据响应码状态定义为错误状态并跳转到设置的默认后端 | []int |
| nginx.ingress.kubernetes.io/default-backend | 自定义默认后端的资源对象 Service 名称,当客户端的请求没有匹配的 Nginx 规则或响应错误时,将被转发到默认后端 | string |
| nginx.ingress.kubernetes.io/whitelist-source-range | 功能同 ConfigMap 配置键 whitelist-source-range | CIDR |
| nginx.ingress.kubernetes.io/permanent-redirect | 设置永久重定向的目标地址 | string |
| nginx.ingress.kubernetes.io/permanent-redirect-code | 自定义永久重定向的响应码,默认为 301 | number |
| nginx.ingress.kubernetes.io/temporal-redirect | 设置临时重定向的目标地址 | string |
| nginx.ingress.kubernetes.io/from-to-www-redirect | 设置是否将当前虚拟主机子域名为 www 的请求跳转到当前主机域名 | true 或 false |
| nginx.ingress.kubernetes.io/rewrite-target | 同 Nginx 配置指令 rewrite | URI |
| nginx.ingress.kubernetes.io/enable-rewrite-log | 同 Nginx 配置指令 rewrite log,默认为 false | true 或 false |
| nginx.ingress.kubernetes.io/mirror-uri | 同 Nginx 配置指令 mirro | true 或 false |
| nginx.ingress.kubernetes.io/mirror-request-body | 同 Nginx 配置指令 mirror_request_body,默认为 true | true 或 false |
访问控制
| 名称 | 描述 | 值 |
|---|---|---|
| nginx.ingress.kubernetes.io/limit-rate | 访问流量速度限制,同 Nginx 配置指令 limit_rate | number |
| nginx.ingress.kubernetes.io/limit-rate-after | 启用访问流量速度限制的最大值,同 Nginx 配置指令 limit_rate_after | number |
| nginx.ingress.kubernetes.io/limit-connections | 节并发连接数限制,同 Nginx 配置指令 limit_conn | number |
| nginx.ingress.kubernetes.io/limit-rps | 每秒请求频率限制,burst 参数为给定值的 5 倍,响应状态码由 ConfigMap 的 limit-req-status-code 设定 | number |
| nginx.ingress.kubernetes.io/limit-rpm | 每分钟请求频率限制,burst 参数为给定值的 5 倍,响应状态码由 ConfigMap 的 limit-req-status-code 设定 | number |
| nginx.ingress.kubernetes.io/limit-whitelist | 对以上限制设置基于 IP 的白名单 | CIDR |
认证管理
Nginx Ingress 提供了基本认证、摘要认证和外部认证 3 种方式,为被代理服务器提供认证支持。认证管理配置说明如下表所示
| 名称 | 描述 | 值 |
|---|---|---|
| nginx.ingress.kubernetes.io/enable-global-auth | 如果 ConfigMap 的 global-auth-url 被设置,Nginx 会将所有的请求重定向到提供身份验证的 URL,默认为 true | true 或 false |
| nginx.ingress.kubernetes.io/satisfy | 同 Nginx 配置指令 satisfy | string |
| nginx.ingress.kubernetes.io/auth-type | 设置 HTTP 认证类型,支持基本和摘要两种类型 | basic 或 digest |
| nginx.ingress.kubernetes.io/auth-secret | 指定关联资源对象 secret 的名称 | string |
| nginx.ingress.kubernetes.io/auth-realm | 设置基本认证的提示信息 auth_basic | string |
| nginx.ingress.kubernetes.io/auth-url | 设置提供外部身份认证的 URL,由 Nginx 配置指令 auth_request 提供该功能 | string |
| nginx.ingress.kubernetes.io/auth-signin | 设置当外部认证返回 401 时跳转的 URL,通常为提示输入用户名和密码的 URL | string |
| nginx.ingress.kubernetes.io/auth-method | 指定访问外部认证 URL 的 HTTP 方法,由 Nginx 配置指令 proxy_method 提供该功能 | string |
| nginx.ingress.kubernetes.io/auth-request-redirect | 设置发送给认证服务器请求头中 X-Auth-Request-Redirect 的值 | string |
| nginx.ingress.kubernetes.io/auth-cache-key | 启用认证缓存,并设置认证缓存的关键字 | string |
| nginx.ingress.kubernetes.io/auth-cache-duration | 基于响应码设置认证缓存的有效时间 | string |
| nginx.ingress.kubernetes.io/auth-response-headers | 设置认证请求完成后传递到真实后端的头信息 | string |
| nginx.ingress.kubernetes.io/auth-snippet | 可以自定义在外部认证指令区域添加 Nginx 配置指令 | string |
跨域访问
| 名称 | 描述 | 值 |
|---|---|---|
| nginx.ingress.kubernetes.io/enable-cors | 是否启用跨域访问支持,默认为 false | true 或 false |
| nginx.ingress.kubernetes.io/cors-allow-origin | 允许跨域访问的域名,默认为 *,表示接受任意域名的访问 | string |
| nginx.ingress.kubernetes.io/cors-allow-methods | 允许跨域访问方法,默认为 GET、PUT、POST、DELETE、PATCH、OPTIONS | string |
| nginx.ingress.kubernetes.io/cors-allow-headers | 允许跨域访问的请求头,默认为 DNT,X-CustomHeader、Keep-Alive、User-Agent、X-Requested-With、If-Modified-Since、Cache-Control、Content-Type、Authorization | string |
| nginx.ingress.kubernetes.io/cors-allow-credentials | 设置在响应头中 Access-Control-Allow-Credentials 的值,设置是否允许客户端携带验证信息,如 cookie 等,默认为 true | true 或 false |
| nginx.ingress.kubernetes.io/cors-max-age | 设置响应头中 Access-Control-Max-Age 的值,设置返回结果可以用于缓存的最长时间,默认为 1728000 秒 | number |
HTTPS配置
| 名称 | 描述 | 值 |
|---|---|---|
| nginx.ingress.kubernetes.io/force-ssl-redirect | 当客户端的 HTTPS 被外部集群进行 SSL 卸载(SSL offloading)时,仍将 HTTP 的请求强制跳转到 HTTPS 端口 | true 或 false |
| nginx.ingress.kubernetes.io/ssl-redirect | 设置当前虚拟主机支持 HTTPS 请求时,是否将 HTTP 的请求强制跳转到 HTTPS 端口,全局默认为 true | true 或 false |
| nginx.ingress.kubernetes.io/ssl-passthrough | 设置是否启用 SSL 透传 | true 或 false |
| nginx.ingress.kubernetes.io/auth-tls-secret | 设置客户端证书的资源对象名称 | string |
| nginx.ingress.kubernetes.io/ssl-ciphers | 设置 TLS 用于协商使用的加密算法组合,同 Nginx 配置指令 ssl_ciphers | string |
| nginx.ingress.kubernetes.io/auth-tls-verify-client | 是否启用客户端证书验证,同 Nginx 配置指令 ssl_verify_client | string |
| nginx.ingress.kubernetes.io/auth-tls-verify-depth | 客户端证书链的验证深度同 Nginx 配置指令 ssl_verify_depth | number |
| nginx.ingress.kubernetes.io/auth-tls-error-page | 设置客户端证书验证错误时的跳转页面 | string |
| nginx.ingress.kubernetes.io/auth-tls-pass-certificate-to-upstream | 指定证书是否传递到上游服务器 | true 或 false |
| nginx.ingress.kubernetes.io/secure-verify-ca-secret | 设置是否启用对被代理服务器的 SSL 证书验证功能 | string |
版权声明:本文为m0_37642477原创文章,遵循 CC 4.0 BY-SA 版权协议,转载请附上原文出处链接和本声明。